By Joseph Kakande, 2011 Marconi Society Young Scholar
This post originally appears on the Marconi Society Blog.
“Being selected as a Young Scholar and interacting with the Marconi Fellows is a constant source of inspiration for dreaming and doing big things.”
Salman Baset, Recognized in 2008, CTO, IBM Security, IBM Blockchain Solutions
“Becoming a Young Scholar has broadened my perspective on how my research benefits humanity.”
Aakanksha Chowdhery, Recognized in 2012, Machine Learning Engineer, Google Brain
“I found the award indispensable in establishing myself and making connections. The publicity generated from the award provided a platform to share my research and to form potential collaborations.“
Joe Lukens, Recognized in 2015, Research Scientist and Wigner Fellow, Oak Ridge National Laboratory
“I’m really honored to be considered worthy of joining the Marconi Society Young Scholars. I think that this award will definitely encourage more women in the region to enter the field of science and to accomplish even greater things.”
Qurrat-Ul-Ain Nadeem, Recognized in 2018, Postdoctoral Research Fellow, University of British Columbia
“I am humbled and honored to be chosen for the Paul Baran Young Scholar Award. It is easier to be known in your own area, but the fact that my work translates to broader audiences in the communications arena makes me very proud. It gives me assurance that I’m moving in the right direction.”
Negar Reiskarimian, Recognized in 2017, Assistant Professor, MIT EECS
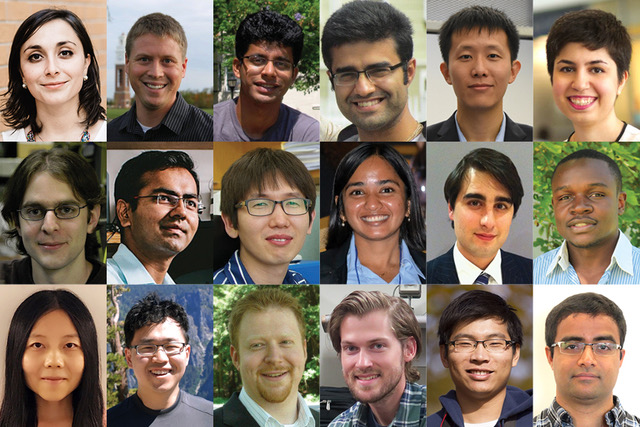
We are 41 strong and come from every continent except Antarctica.
We studied at universities ranging from Telecomm ParisTech to The Technion to King Abdullah University of Science and Technology to Stanford to KAIST.
We have all had the good fortune to have had a professor, advisor or mentor with the foresight and generosity to nominate us for the career-changing Marconi Society Young Scholar award.
For me personally – and for others receiving this prestigious award – being a Marconi Society Paul Baran Young Scholar is a game-changer.
When Gioia Marconi Braga, Guglielmo Marconi’s daughter, formed the society in 1974, it was called the Marconi International Fellowship Foundation. Gioia envisioned this group as a true community of colleagues with a shared passion for both intellectual achievements and “recognizing and sustaining those spiritual aspirations that a creative thinker may wish to apply to the establishment of a better world in which to live.”
Young Scholars not only get meet the luminaries in our fields – we are privileged to be treated like family by these legends of communications. In my case, this has meant job offers, valuable counsel and introductions for my startup and leadership opportunities to work closely with Marconi Fellows on the board and on various projects.
The Young Scholar cohort is an exceptional group of likeminded innovators. While we studied different areas of communications in different parts of the world, many of us share a passion for social impact and leveraging technology to bring the power of the network to everyone, particularly the half of the world that does not have access today. It has been gratifying for me to discover that shared vision and work with other Young Scholars to bring the Celestini Program to life, offering resources and support to technical undergrads in emerging nations to give them hands-on experience solving critical local issues through telecommunications network innovations.
As Gioia intended, my relationships with the Marconi Society extend far beyond work and academics. The Young Scholars, Fellows and staff have become true friends and part of my community, taking part in some of my most important life events.
If you are an academic or business leader who knows an exceptionally talented young researcher in information and communications technology, I urge you to nominate him or her. And if you think you are a candidate for a Marconi Society Young Scholar award, please ask for a nomination.
Nominations will be accepted from February 1 through May 15, 2020. We seek gender, discipline and geographic diversity.
Take the time to make a true difference in a young researcher’s career.
